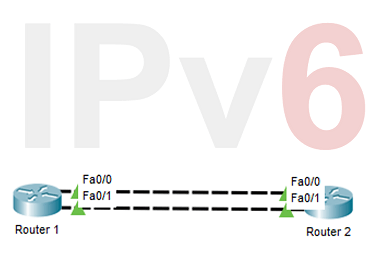
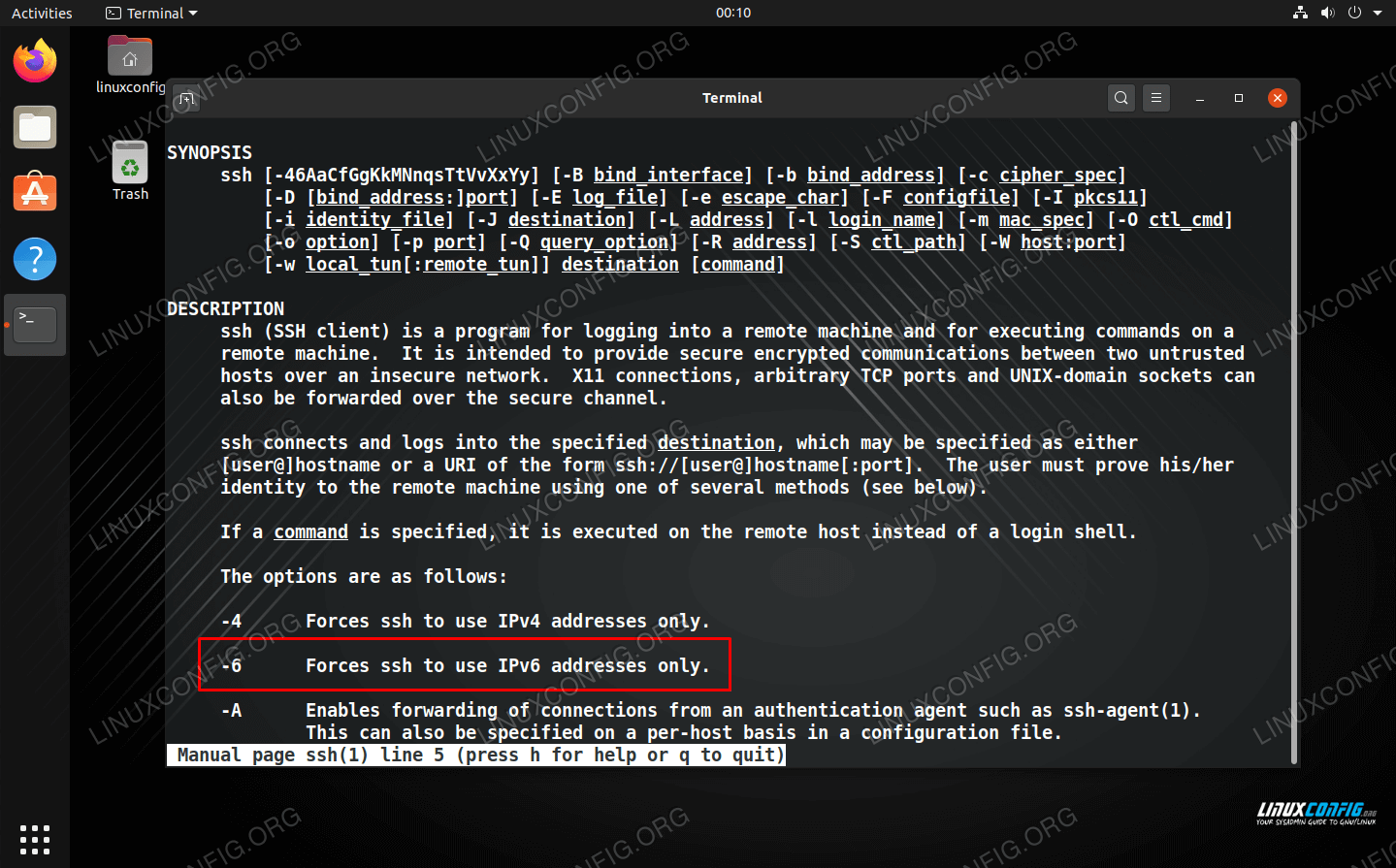
Introduction to IPv6 Addresses: How to Use and How to Explore the Network (Part 1) - Ethical hacking and penetration testing
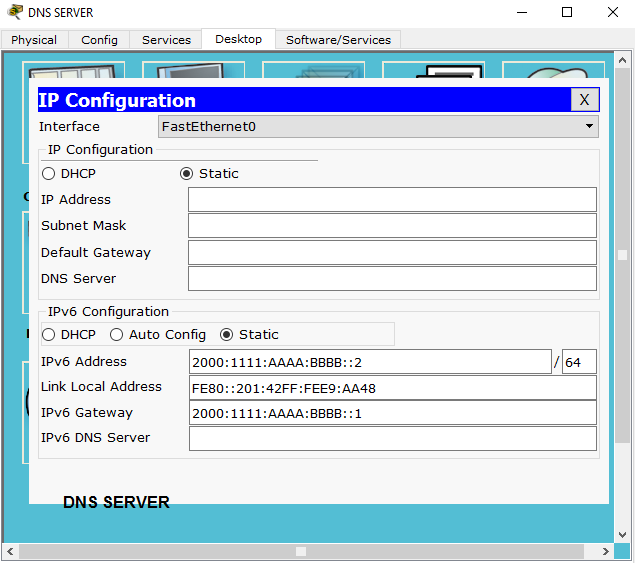
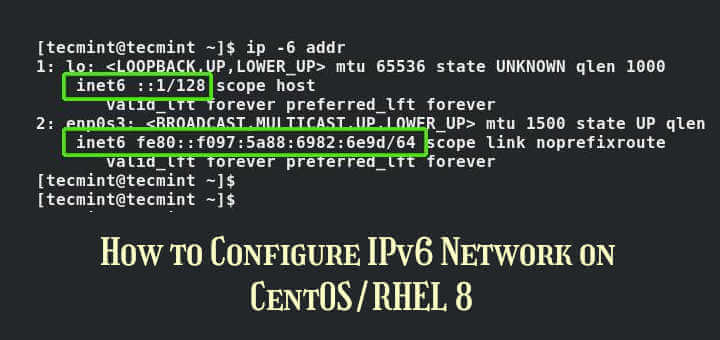
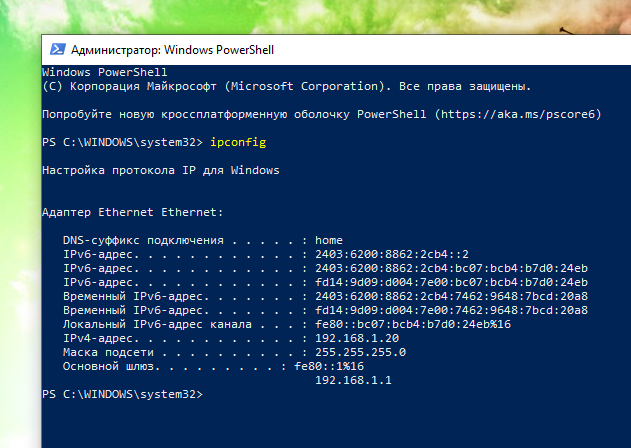
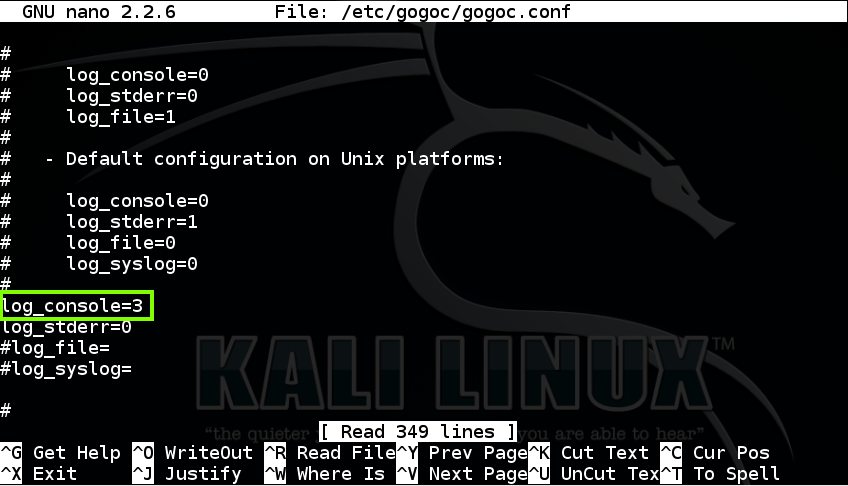
Deploy and Configure DHCPv6 Dynamic Host Configuration Protocol for IPv6 | Learn Linux CCNA CEH IPv6 Cyber-Security Online
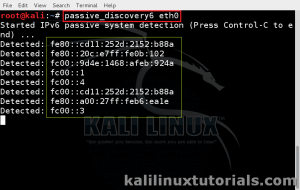
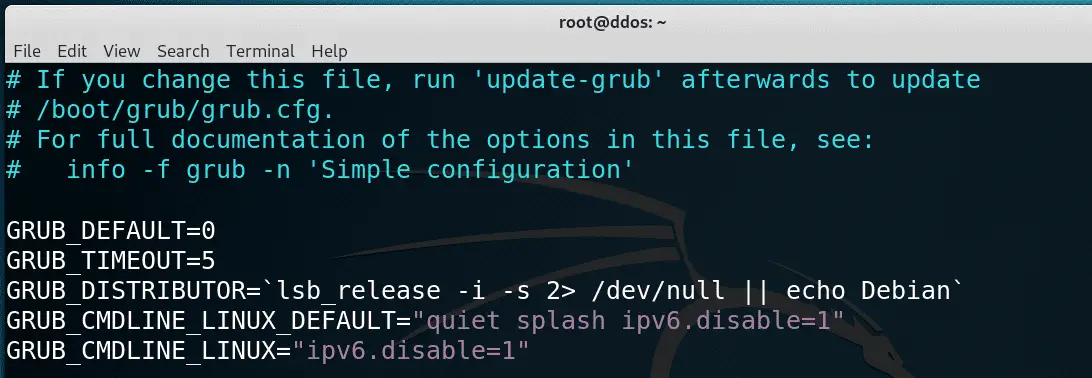
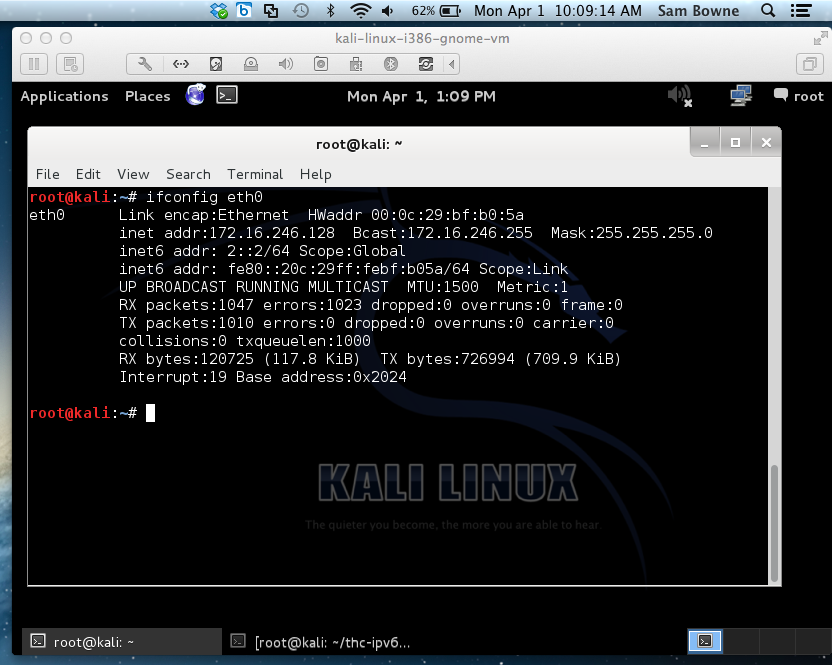
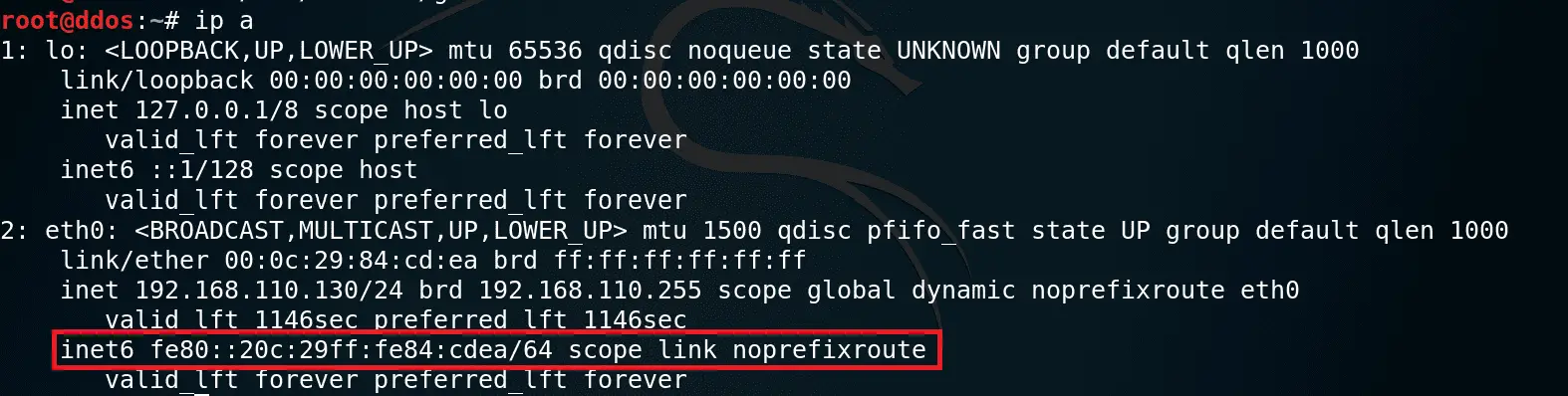
Discover IPv6 Network Range & Hosts from an IPv6 Enabled Network Using passive_discovery6 - Kali Linux Tutorials


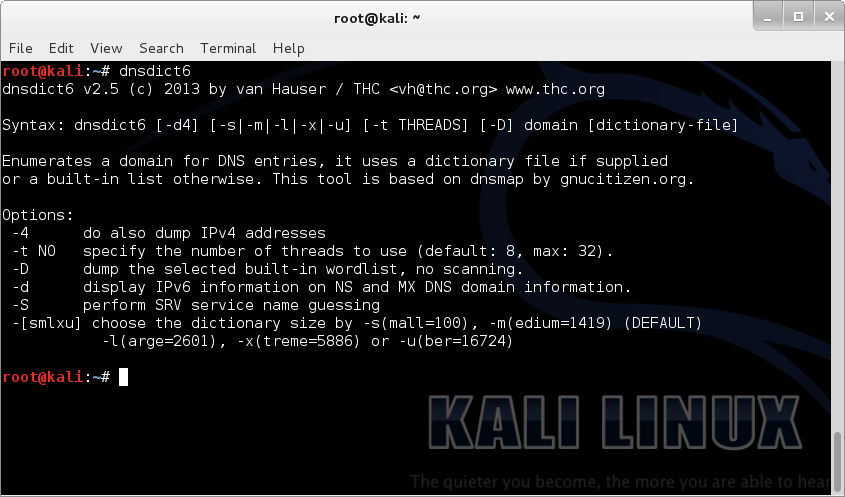
![DNSDict6: Parallized DNS IPv6 Dictionary Bruteforcer [Kali Linux] - YouTube DNSDict6: Parallized DNS IPv6 Dictionary Bruteforcer [Kali Linux] - YouTube](https://i.ytimg.com/vi/hZu5Np1RoNw/maxresdefault.jpg)