Applied Sciences | Free Full-Text | A Graph-Based Differentially Private Algorithm for Mining Frequent Sequential Patterns
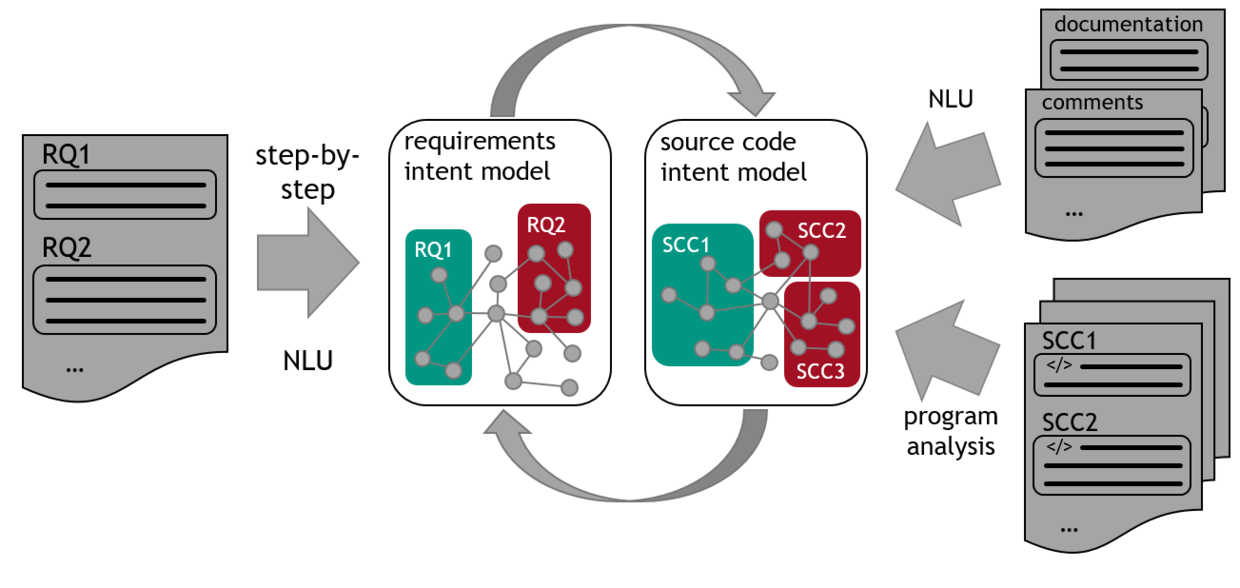
KIT - IPD Tichy - Core competences - Projects - INDIRECT: Intent-driven Requirements-to-Code Traceability

Methodology for acute lymphoblastic leukemia (ALL) image classification | Download Scientific Diagram
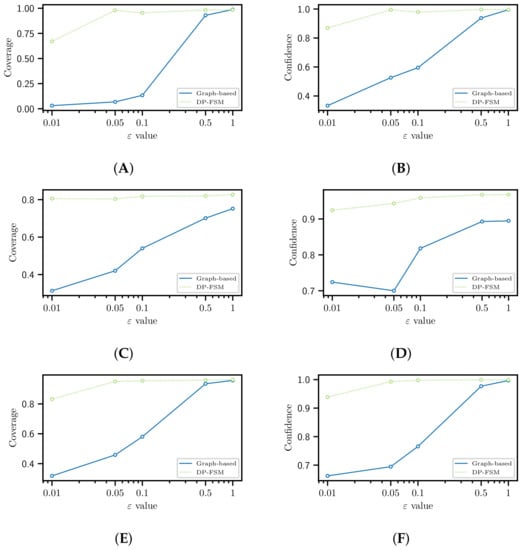
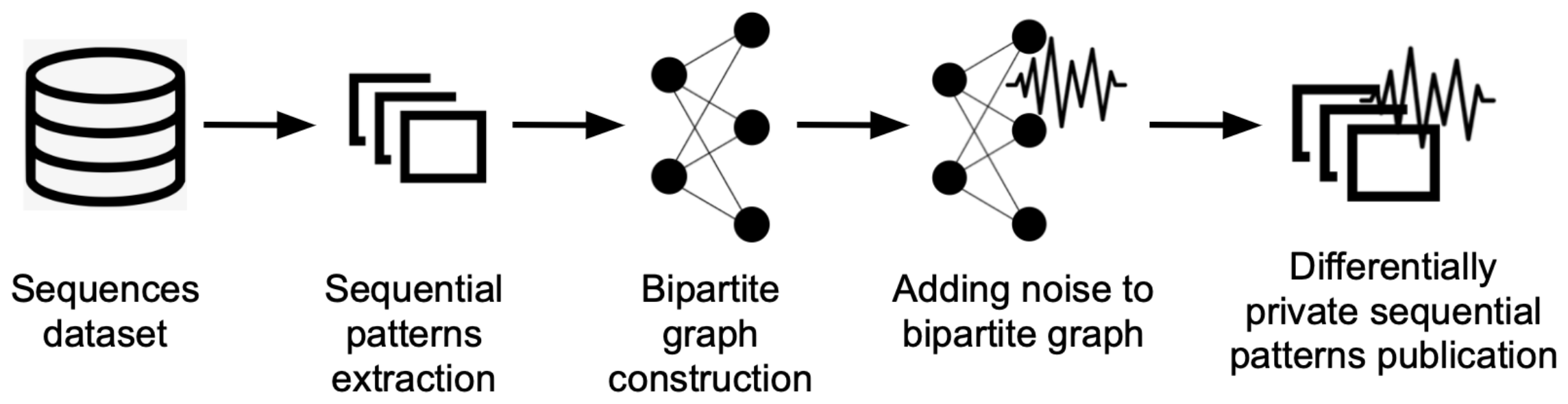
Applied Sciences | Free Full-Text | A Graph-Based Differentially Private Algorithm for Mining Frequent Sequential Patterns

DE112006002892T5 - Systems and methods for switching between autonomous and manual operation of a vehicle - Google Patents

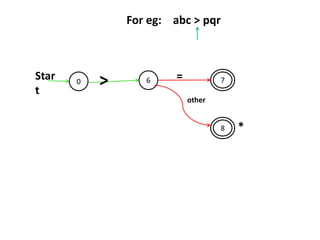
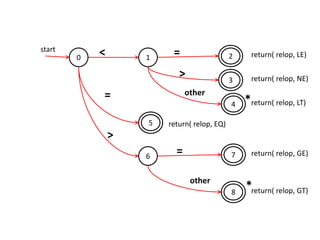
Recognizing Fake identities in Online Social Networks based on a Finite Automaton approach | Semantic Scholar

Energies | Free Full-Text | Accessible Modeling of the German Energy Transition: An Open, Compact, and Validated Model

PDF) Proceedings Fourth International Symposium on Games, Automata, Logics and Formal Verification | Tiziano Villa - Academia.edu

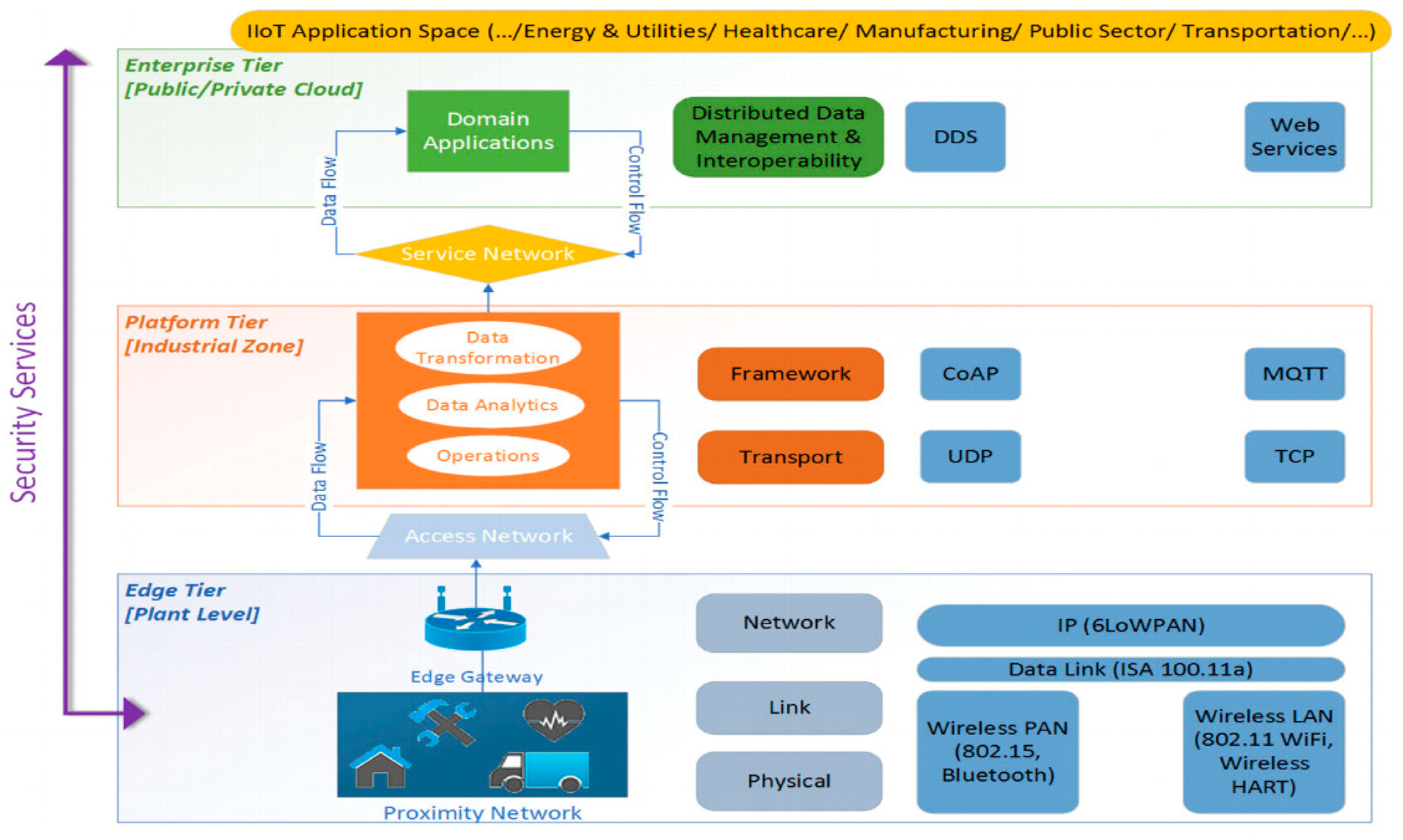
CADEN: cellular automata and DNA based secure framework for privacy preserving in IoT based healthcare | SpringerLink
ICT-32-2014: Cybersecurity, Trustworthy ICT WITDOM “empoWering prIvacy and securiTy in non-trusteD envirOnMents” D3.5 – WI
![PDF] SQuAD2-CR: Semi-supervised Annotation for Cause and Rationales for Unanswerability in SQuAD 2.0 | Semantic Scholar PDF] SQuAD2-CR: Semi-supervised Annotation for Cause and Rationales for Unanswerability in SQuAD 2.0 | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/62b9e3e864e31fe8010e3c804f44ff85b401fcd1/7-Table5-1.png)
PDF] SQuAD2-CR: Semi-supervised Annotation for Cause and Rationales for Unanswerability in SQuAD 2.0 | Semantic Scholar

Application layer classification of Internet traffic using ensemble learning models - Arfeen - 2021 - International Journal of Network Management - Wiley Online Library
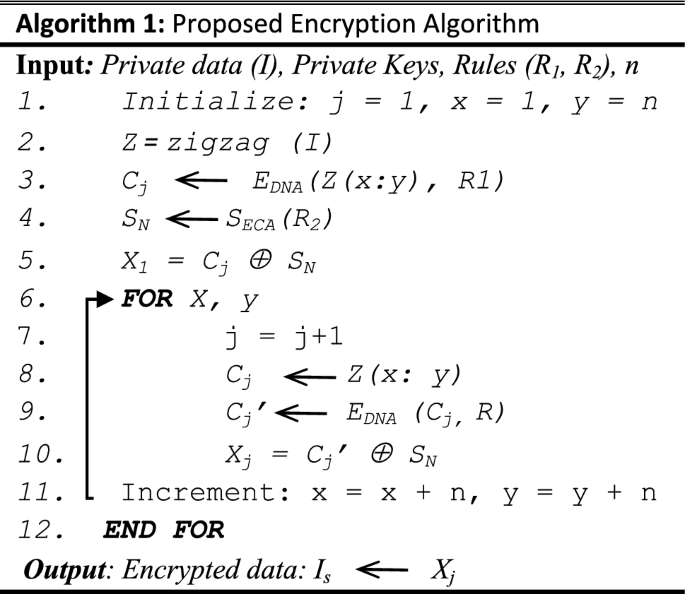
CADEN: cellular automata and DNA based secure framework for privacy preserving in IoT based healthcare | SpringerLink